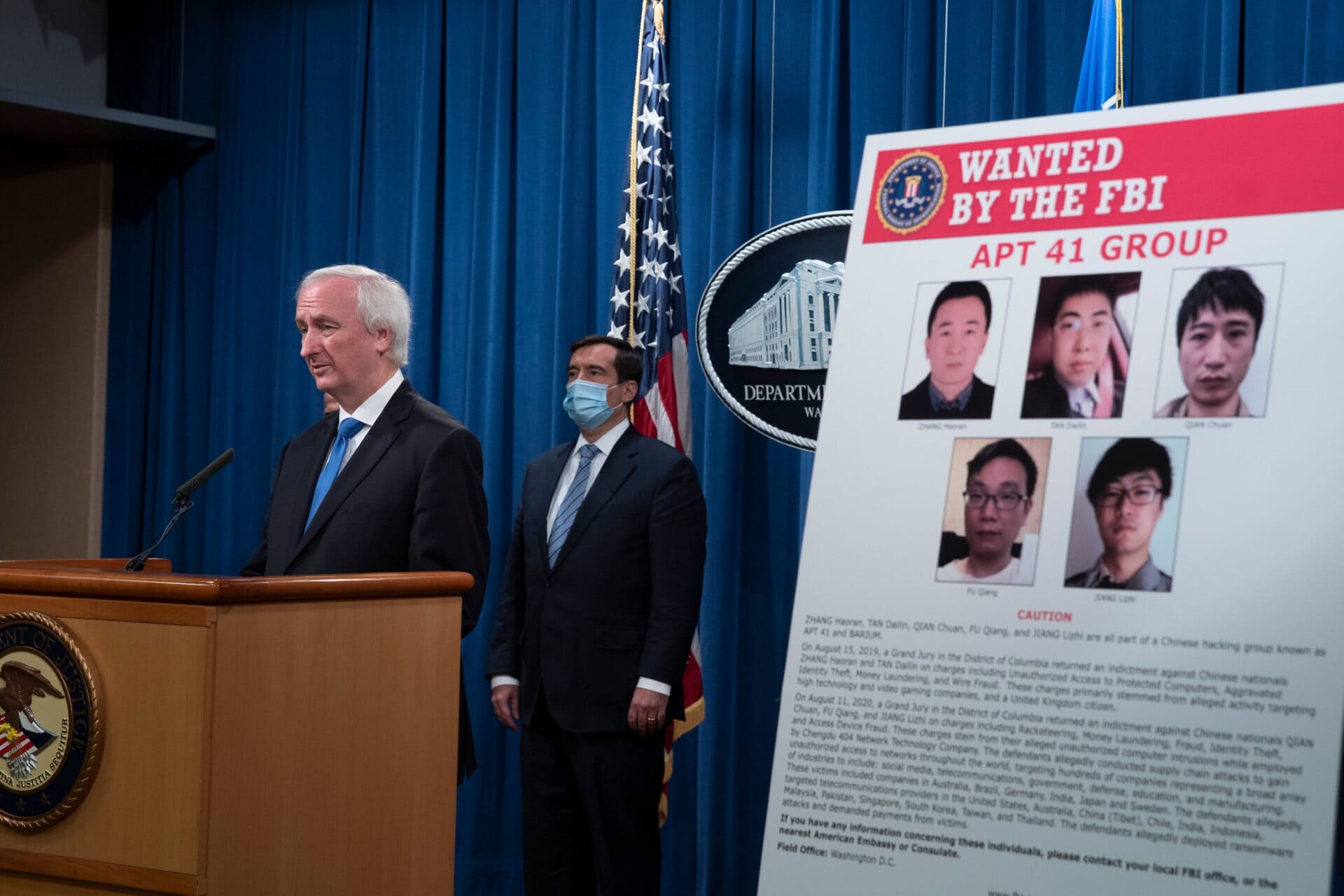
Mapping Chinese APTs
Analyzing the tactics, targets, and evolution of China-linked advanced persistent threat groups targeting U.S. critical infrastructure, defense systems, and sensitive data.
The Typhoon Campaign
Salt Typhoon’s compromise of major U.S. telecom providers revealed the depth of Chinese cyber penetration into American infrastructure. But Salt Typhoon is only one element of a broader campaign. Volt Typhoon pre-positions for disruptions of critical systems. Flax Typhoon builds botnets from compromised devices. This project provides comprehensive mapping of the threat groups, their techniques, and their strategic objectives.
Policy Gaps
Despite billions spent on cybersecurity, CCP-linked APTs continue to achieve access to the most sensitive U.S. systems. Our analysis identifies where current policy and regulatory frameworks fail to address the threat, what incentive structures might improve private sector security practices, and what government responses have been proven ineffective.